Prevent XSS Vulnerability
| 开发者 | sasiddiqui |
|---|---|
| 更新时间 | 2025年7月22日 22:10 |
| PHP版本: | 3.5 及以上 |
| WordPress版本: | 6.8 |
| 版权: | GPLv3 |
| 版权网址: | 版权信息 |
详情介绍:
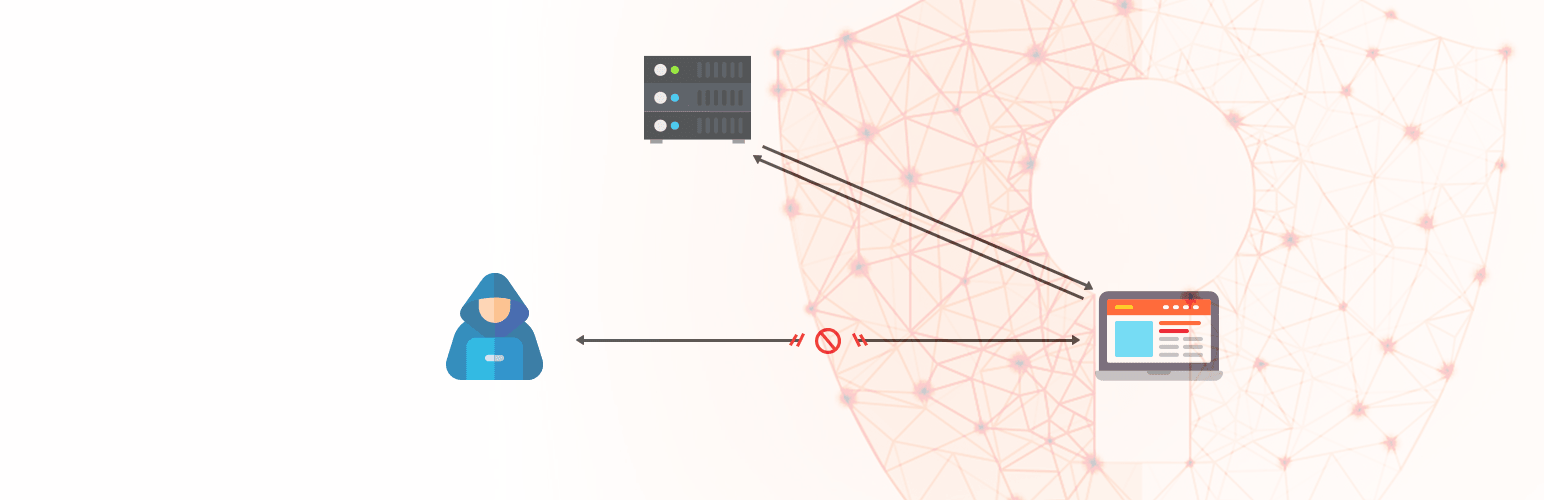
This plugin helps protect your website from two common types of Cross-Site Scripting (XSS) vulnerabilities:
- Reflected XSS: This happens when harmful scripts are hidden in a website's URL. If a user clicks a link with such a script, it can run in their browser, potentially stealing their data or taking control of their system.
- Self-XSS: This occurs when a user's own input on your website is displayed back to them in an unsafe way, allowing malicious scripts to run in their browser.
- Opening Round Bracket
( - Closing Round Bracket
) - Less than Sign
< - Greater than Sign
> - Opening Square Bracket
[ - Closing Square Bracket
] - Opening Curly Bracket
{ - Pipe or Vertical Bar
| - Closing Curly Bracket
}
- Exclamation Mark
! - Double Quotation
" - Single Quotation
' - Opening Round Bracket
( - Closing Round Bracket
) - Asterisk Sign
* - Less than Sign
< - Greater than Sign
> - Grave Accent `
- Caret
^ - Opening Square Bracket
[ - Closing Square Bracket
] - Opening Curly Bracket
{ - Pipe or Vertical Bar
| - Closing Curly Bracket
}
$_GET: This plugin automatically makes HTML characters safe within the $_GET variable. This is vital if your website pulls data from URLs and displays it as part of your web page. It helps prevent malicious scripts from being injected through user-provided input.
安装:
You can install this plugin either through your WordPress dashboard or manually via FTP.
From within WordPress
- Go to 'Plugins > Add New'.
- Search for "Prevent XSS Vulnerability".
- Click "Activate" for "Prevent XSS Vulnerability" on your Plugins page.
- Then, follow the "After activation" steps below.
- Upload the
prevent-xss-vulnerabilityfolder to the/wp-content/plugins/directory. - Activate "Prevent XSS Vulnerability" from the 'Plugins' menu in WordPress.
- Then, follow the "After activation" steps below.
- Go to the
Prevent XSS Vulnerabilitypage in your WordPress Admin Dashboard. - Adjust the settings to fit your website's needs.
- That's it! You're done.
常见问题:
Q. Why should I install this plugin?
A. Installing this plugin is the easiest way to protect your site from XSS vulnerabilities.
Q. Does this plugin escape HTML when printing search results?
A. Yes, this plugin escapes HTML in the $_GET variable, which is often used to display data from the URL in HTML. However, if your site heavily relies on $_GET for other functions, you might need to do thorough testing to ensure everything works correctly.
Q. Does this plugin conflict with any other plugins?
A. While we haven't received reports of major conflicts, it's always a good idea to thoroughly test your website after installing any new plugin.
更新日志:
2.1.0 - July 03, 2025
- Key Changes & Improvements:
- Enhanced Console Visibility: The prominent "Stop!" message now appears in a much larger (48px), bold, red font with a black text shadow to grab immediate attention. The main warning message also uses a larger, more readable font (20px).
- Improved Console Grouping: The entire Self-XSS warning is now grouped within a
console.group('Self-XSS Warning')block. This keeps all related messages together in the developer console, making the warning stand out and preventing it from getting lost among other console output.
- For a detailed changelog of earlier versions, please refer to the separate
changelog.txtfile.