Two Factor
| 开发者 |
georgestephanis
valendesigns stevenkword extendwings sgrant aaroncampbell johnbillion stevegrunwell netweb kasparsd alihusnainarshad passoniate |
|---|---|
| 更新时间 | 2026年2月17日 21:21 |
| WordPress版本: | 6.9 |
| 版权: | GPL-2.0-or-later |
| 版权网址: | 版权信息 |
详情介绍:
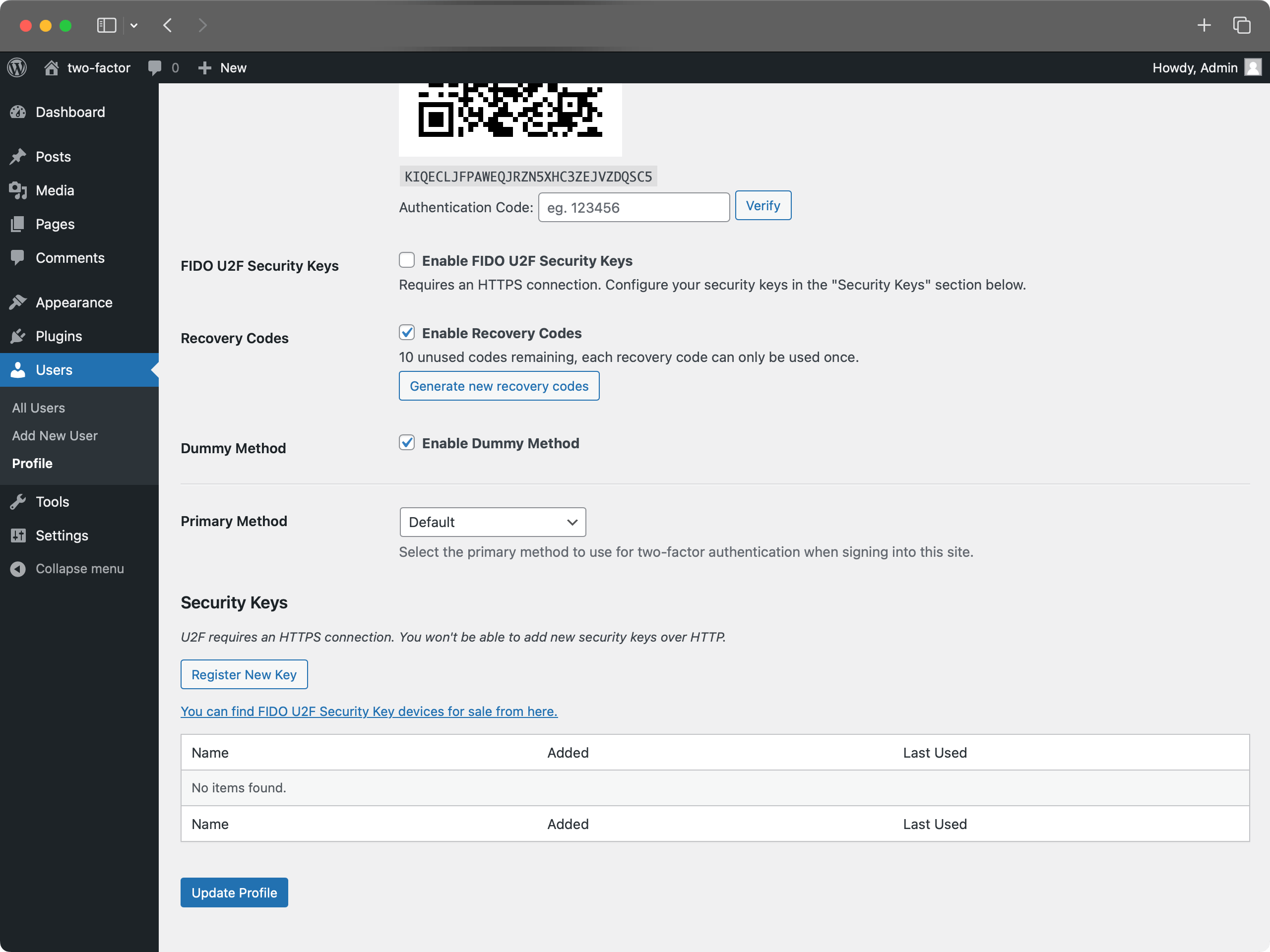
- Navigate to your profile: Go to "Users" → "Your Profile" in the WordPress admin
- Find Two-Factor Options: Scroll down to the "Two-Factor Options" section
- Choose your methods: Enable one or more authentication providers (noting a site admin may have hidden one or more so what is available could vary):
- Authenticator App (TOTP) - Use apps like Google Authenticator, Authy, or 1Password
- Email Codes - Receive one-time codes via email
- FIDO U2F Security Keys - Use physical security keys (requires HTTPS)
- Backup Codes - Generate one-time backup codes for emergencies
- Dummy Method - For testing purposes only (requires WP_DEBUG)
- Configure each method: Follow the setup instructions for each enabled provider
- Set primary method: Choose which method to use as your default authentication
- Save changes: Click "Update Profile" to save your settings
- No global settings: This plugin operates on a per-user basis only. For more, see GH#249.
- User management: Administrators can configure 2FA for other users by editing their profiles
- Security recommendations: Encourage users to enable backup methods to prevent account lockouts
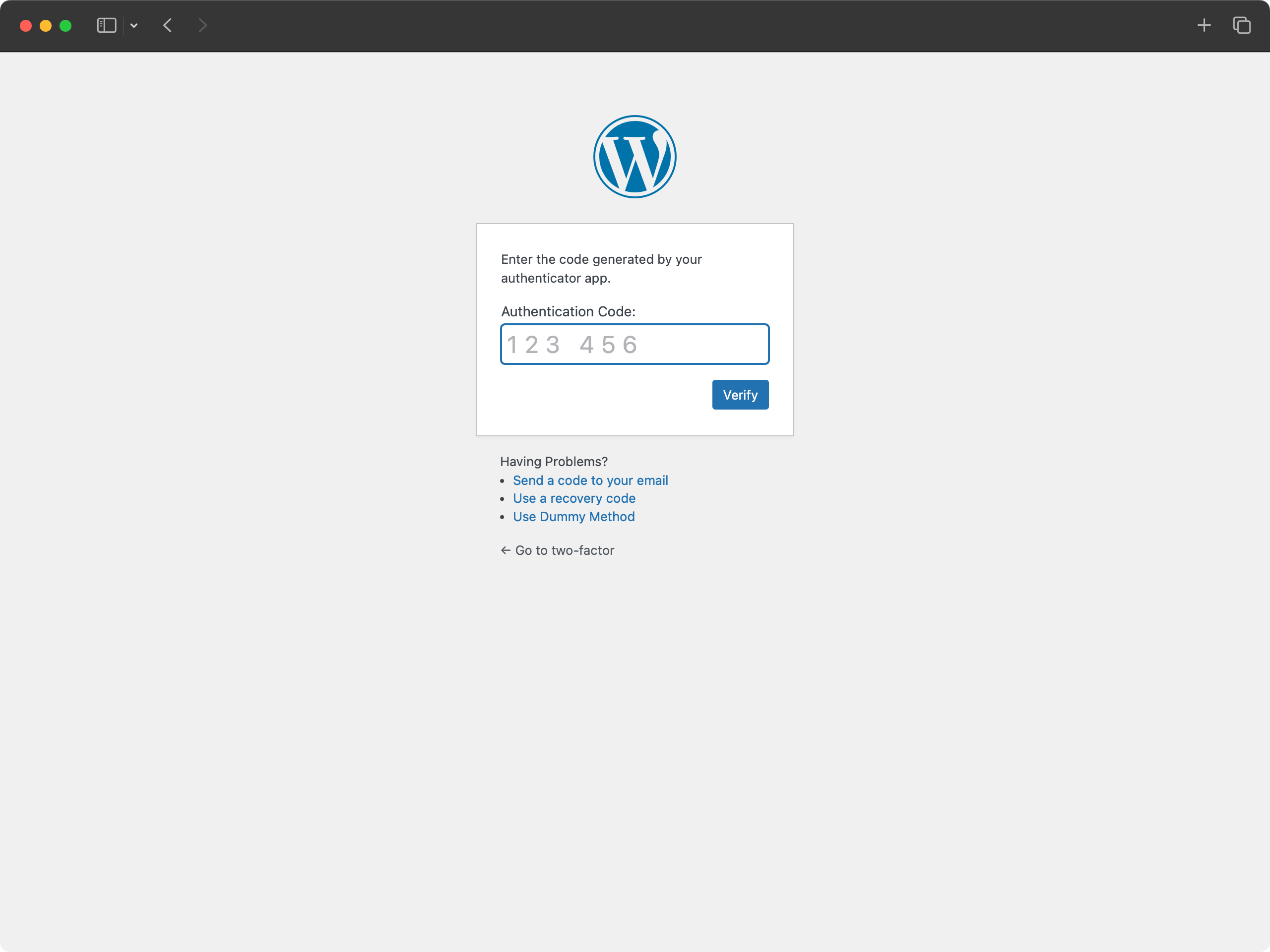
- Security: High - Time-based one-time passwords
- Setup: Scan QR code with authenticator app
- Compatibility: Works with Google Authenticator, Authy, 1Password, and other TOTP apps
- Best for: Most users, provides excellent security with good usability
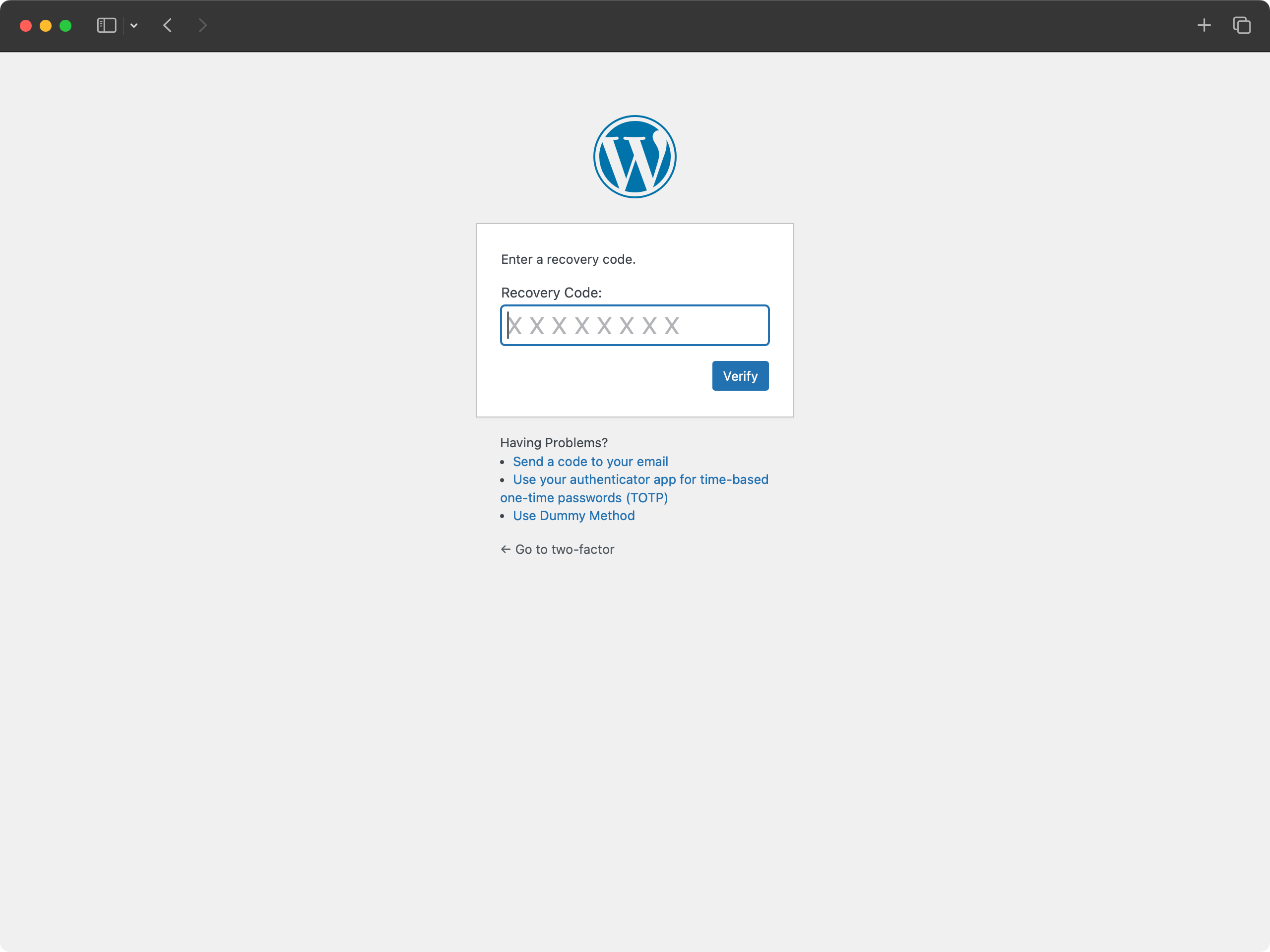
- Security: Medium - One-time use codes
- Setup: Generate 10 backup codes for emergency access
- Compatibility: Works everywhere, no special hardware needed
- Best for: Emergency access when other methods are unavailable
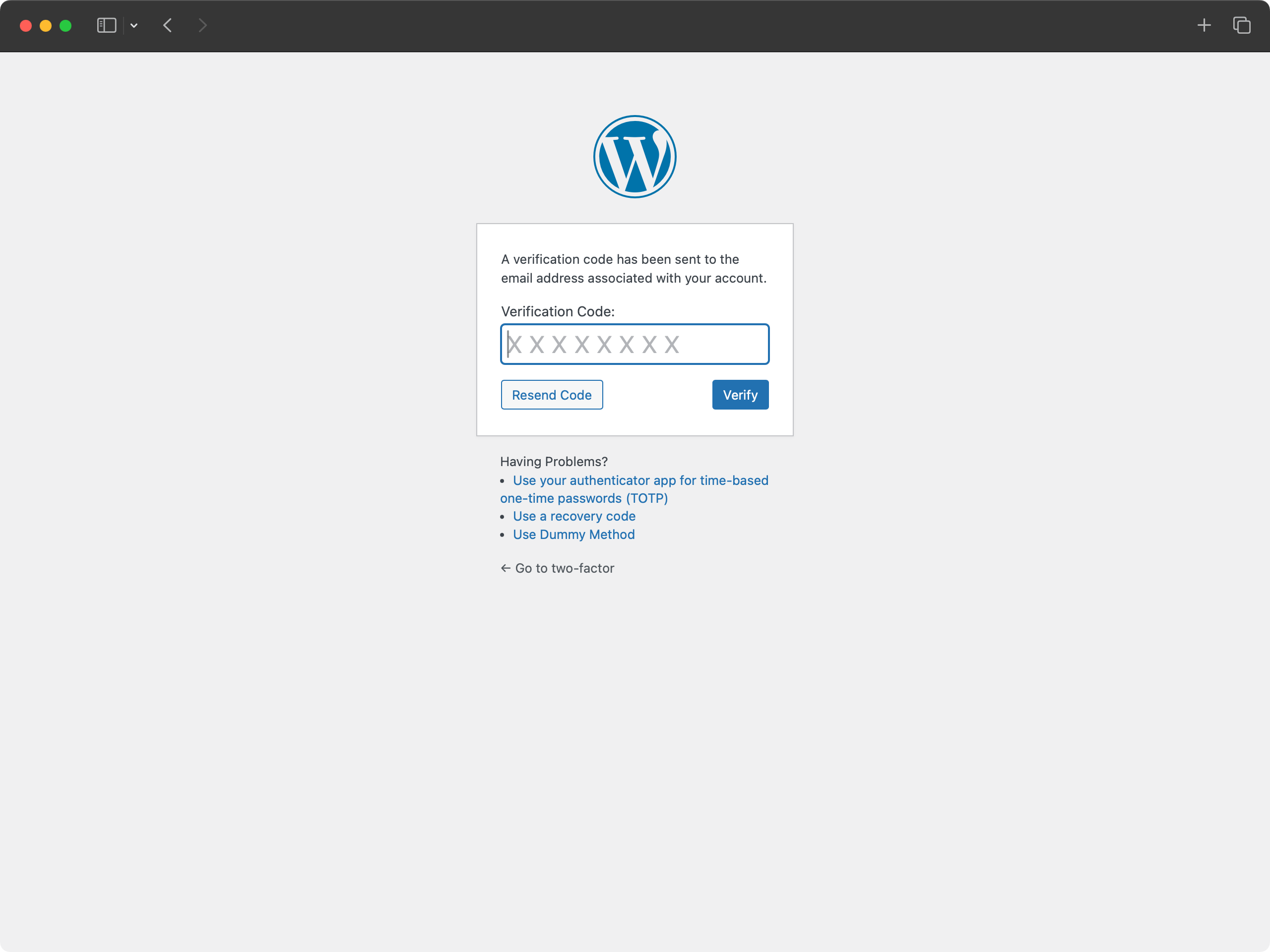
- Security: Medium - One-time codes sent via email
- Setup: Automatic - uses your WordPress email address
- Compatibility: Works with any email-capable device
- Best for: Users who prefer email-based authentication
- Security: High - Hardware-based authentication
- Setup: Register physical security keys (USB, NFC, or Bluetooth)
- Requirements: HTTPS connection required, compatible browser needed
- Browser Support: Chrome, Firefox, Edge (varies by key type)
- Best for: Users with security keys who want maximum security
- Security: None - Always succeeds
- Setup: Only available when WP_DEBUG is enabled
- Purpose: Testing and development only
- Best for: Developers testing the plugin
- FIDO U2F Security Keys require an HTTPS connection to function
- Other methods work on both HTTP and HTTPS sites
- FIDO U2F requires a compatible browser and may not work on all devices
- TOTP and email methods work on all devices and browsers
- Always enable backup codes to prevent being locked out of your account
- If you lose access to all authentication methods, contact your site administrator
- Use multiple authentication methods when possible
- Keep backup codes in a secure location
- Regularly review and update your authentication settings For more information about two-factor authentication in WordPress, see the WordPress Advanced Administration Security Guide.
two_factor_providersfilter overrides the available two-factor providers such as email and time-based one-time passwords. Array values are PHP classnames of the two-factor providers.two_factor_providers_for_userfilter overrides the available two-factor providers for a specific user. Array values are instances of provider classes and the user objectWP_Useris available as the second argument.two_factor_enabled_providers_for_userfilter overrides the list of two-factor providers enabled for a user. First argument is an array of enabled provider classnames as values, the second argument is the user ID.two_factor_user_authenticatedaction which receives the logged inWP_Userobject as the first argument for determining the logged in user right after the authentication workflow.two_factor_user_api_login_enablefilter restricts authentication for REST API and XML-RPC to application passwords only. Provides the user ID as the second argument.two_factor_email_token_ttlfilter overrides the time interval in seconds that an email token is considered after generation. Accepts the time in seconds as the first argument and the ID of theWP_Userobject being authenticated.two_factor_email_token_lengthfilter overrides the default 8 character count for email tokens.two_factor_backup_code_lengthfilter overrides the default 8 character count for backup codes. Provides theWP_Userof the associated user as the second argument.two_factor_rest_api_can_edit_userfilter overrides whether a user’s Two-Factor settings can be edited via the REST API. First argument is the current$can_editboolean, the second argument is the user ID.two_factor_before_authentication_promptaction which receives the provider object and fires prior to the prompt shown on the authentication input form.two_factor_after_authentication_promptaction which receives the provider object and fires after the prompt shown on the authentication input form.two_factor_after_authentication_inputaction which receives the provider object and fires after the input shown on the authentication input form (if form contains no input, action fires immediately aftertwo_factor_after_authentication_prompt).
屏幕截图:
常见问题:
What PHP and WordPress versions does the Two-Factor plugin support?
This plugin supports the last two major versions of WordPress and the minimum PHP version supported by those WordPress versions.
我该如何发送反馈或获取有关错误的帮助?
报告漏洞、功能建议或任何其他(非安全相关)的反馈最佳途径是在 GitHub Two Factor 的 issues 页面。在提交新问题之前,请搜索现有问题以检查是否有其他人报告了相同的反馈。
我应该在哪里报告安全漏洞?
插件贡献者和 WordPress 社区非常重视安全漏洞。我们感谢您负责任地披露您发现的漏洞,并将竭尽全力解决您的贡献。 To report a security issue, please visit the WordPress HackerOne program.
Why doesn't this plugin have site-wide settings?
This plugin is designed to work on a per-user basis, allowing each user to choose their preferred authentication methods. This approach provides maximum flexibility and security. Site administrators can still configure 2FA for other users by editing their profiles. For more information, see issue #437.
What if I lose access to all my authentication methods?
If you have backup codes enabled, you can use one of those to regain access. If you don't have backup codes or have used them all, you'll need to contact your site administrator to reset your account. This is why it's important to always enable backup codes and keep them in a secure location.
Can I use this plugin with WebAuthn?
The plugin currently supports FIDO U2F, which is the predecessor to WebAuthn. For full WebAuthn support, you may want to look into additional plugins that extend this functionality. The current U2F implementation requires HTTPS and has browser compatibility limitations.
Is there a recommended way to use passkeys or hardware security keys with Two-Factor?
Yes. For passkeys and hardware security keys, you can install the Two-Factor Provider: WebAuthn plugin: https://wordpress.org/plugins/two-factor-provider-webauthn/ . It integrates directly with Two-Factor and adds WebAuthn-based authentication as an additional two-factor option for users.
更新日志:
- Breaking Changes: Trigger two-factor flow only when expected by @kasparsd in #660 and #793.
- New Features: Include user IP address and contextual warning in two-factor code emails by @todeveni in #728
- New Features: Optimize email text for TOTP by @masteradhoc in #789
- New Features: Add "Settings" action link to plugin list for quick access to profile by @hardikRathi in #740
- New Features: Additional form hooks by @eric-michel in #742
- New Features: Full RFC6238 Compatibility by @ericmann in #656
- New Features: Consistent user experience for TOTP setup by @kasparsd in #792
- Documentation:
@sincedocs by @masteradhoc in #781 - Documentation: Update user and admin docs, prepare for more screenshots by @jeffpaul in #701
- Documentation: Add changelog & credits, update release notes by @jeffpaul in #696
- Documentation: Clear readme.txt by @masteradhoc in #785
- Documentation: Add date and time information above TOTP setup instructions by @masteradhoc in #772
- Documentation: Clarify TOTP setup instructions by @masteradhoc in #763
- Documentation: Update RELEASING.md by @jeffpaul in #787
- Development Updates: Pause deploys to SVN trunk for merges to
masterby @kasparsd in #738 - Development Updates: Fix CI checks for PHP compatability by @kasparsd in #739
- Development Updates: Fix Playground refs by @kasparsd in #744
- Development Updates: Persist existing translations when introducing new helper text in emails by @kasparsd in #745
- Development Updates: Fix
missing_direct_file_access_protectionby @masteradhoc in #760 - Development Updates: Fix
mismatched_plugin_nameby @masteradhoc in #754 - Development Updates: Introduce Props Bot workflow by @jeffpaul in #749
- Development Updates: Plugin Check: Fix Missing $domain parameter by @masteradhoc in #753
- Development Updates: Tests: Update to supported WP version 6.8 by @masteradhoc in #770
- Development Updates: Fix PHP 8.5 deprecated message by @masteradhoc in #762
- Development Updates: Exclude 7.2 and 7.3 checks against trunk by @masteradhoc in #769
- Development Updates: Fix Plugin Check errors:
MissingTranslatorsComment&MissingSingularPlaceholderby @masteradhoc in #758 - Development Updates: Add PHP 8.5 tests for latest and trunk version of WP by @masteradhoc in #771
- Development Updates: Add
phpcs:ignorefor falsepositives by @masteradhoc in #777 - Development Updates: Fix(totp):
otpauthlink in QR code URL by @sjinks in #784 - Development Updates: Update deploy.yml by @masteradhoc in #773
- Development Updates: Update required WordPress Version by @masteradhoc in #765
- Development Updates: Fix: ensure execution stops after redirects by @sjinks in #786
- Development Updates: Fix
WordPress.Security.EscapeOutput.OutputNotEscapederrors by @masteradhoc in #776 - Dependency Updates: Bump qs and express by @dependabot[bot] in #746
- Dependency Updates: Bump lodash from 4.17.21 to 4.17.23 by @dependabot[bot] in #750
- Dependency Updates: Bump lodash-es from 4.17.21 to 4.17.23 by @dependabot[bot] in #748
- Dependency Updates: Bump phpunit/phpunit from 8.5.44 to 8.5.52 by @dependabot[bot] in #755
- Dependency Updates: Bump symfony/process from 5.4.47 to 5.4.51 by @dependabot[bot] in #756
- Dependency Updates: Bump qs and body-parser by @dependabot[bot] in #782
- Dependency Updates: Bump webpack from 5.101.3 to 5.105.0 by @dependabot[bot] in #780
- New Features: Add filter for rest_api_can_edit_user_and_update_two_factor_options by @gutobenn in #689
- Development Updates: Remove Coveralls tooling and add inline coverage report by @kasparsd in #717
- Development Updates: Update blueprint path to pull from main branch instead of a deleted f… by @georgestephanis in #719
- Development Updates: Fix blueprint and wporg asset deploys by @kasparsd in #734
- Development Updates: Upload release only on tag releases by @kasparsd in #735
- Development Updates: Bump playwright and @playwright/test by @dependabot[bot] in #721
- Development Updates: Bump tar-fs from 3.1.0 to 3.1.1 by @dependabot[bot] in #720
- Development Updates: Bump node-forge from 1.3.1 to 1.3.2 by @dependabot[bot] in #724
- Development Updates: Bump js-yaml by @dependabot[bot] in #725
- Development Updates: Mark as tested with the latest WP core version by @kasparsd in #730
- Don't URI encode the TOTP url for display. by @dd32 in #711
- Removed the duplicate Security.md by @slvignesh05 in #712
- Fixed linting issues by @sudar in #707
- Update development dependencies and fix failing QR unit test by @kasparsd in #714
- Trigger checkbox js change event by @gedeminas in #688
- Features: Enable Application Passwords for REST API and XML-RPC authentication (by default) by @joostdekeijzer in #697 and #698. Previously this required two_factor_user_api_login_enable filter to be set to true which is now the default during application password auth. XML-RPC login is still disabled for regular user passwords.
- Features: Label recommended methods to simplify the configuration by @kasparsd in #676 and #675
- Documentation: Add WP.org plugin demo by @kasparsd in #667
- Documentation: Document supported versions of WP core and PHP by @jeffpaul in #695
- Documentation: Document the release process by @jeffpaul in #684
- Tooling: Remove duplicate WP.org screenshots and graphics from SVN trunk by @jeffpaul in #683
- Add two_factor_providers_for_user filter to limit two-factor providers available to each user by @kasparsd in #669
- Update automated testing to cover PHP 8.4 and default to PHP 8.3 by @BrookeDot in #665